An ongoing phishing marketing campaign abuses a bit‑recognized characteristic in Microsoft 365 referred to as “Direct Ship” to evade detection by e-mail safety and steal credentials.
Direct Ship is a Microsoft 365 characteristic that permits on‑premises gadgets, purposes, or cloud companies to ship emails via a tenant’s good host as in the event that they originated from the group’s area. It’s designed to be used by printers, scanners, and different gadgets that must ship messages on behalf of the corporate.
Nevertheless, the characteristic is a recognized safety threat, because it would not require any authentication, permitting distant customers to ship inside‑wanting emails from the corporate’s area.
Microsoft recommends that solely superior prospects make the most of the characteristic, as its security is determined by whether or not Microsoft 365 is configured appropriately and the good host is correctly locked down..
“We suggest Direct Ship just for superior prospects prepared to tackle the tasks of e-mail server admins,” explains Microsoft.
“You might want to be accustomed to organising and following finest practices for sending e-mail over the web. When appropriately configured and managed, Direct Ship is a safe and viable choice. However prospects run the chance of misconfiguration that disrupts mail move or threatens the safety of their communication.”
The corporate has shared methods to disable the characteristic, that are defined later within the article, and says they’re engaged on a method to deprecate the characteristic.
Direct Ship abused in a phishing marketing campaign
The phishing marketing campaign was found by the Varonis Managed Information Detection and Response (MDDR) group, who informed BleepingComputer that it’s focusing on greater than 70 organizations throughout all industries, with 95% of the victims primarily based in the US.
Varonis says the marketing campaign began in Could 2025, with over 95% of the focused firms primarily based in the US.
“Victims occupy all kinds of enterprise verticals however over 90% of recognized targets function throughout the Monetary Companies, Development, Engineering, Manufacturing, Healthcare, and Insurance coverage house,” Joseph Avanzato, Safety Operations and Forensics Group Chief, informed BleepingComputer.
“Monetary Companies had been the most typical goal adopted by Manufacturing, Development/Engineering and Healthcare/Insurance coverage.”
The Varonis report explains that the assaults are delivered by way of PowerShell utilizing a focused firm’s good host (company-com.mail.safety.outlook.com), making it potential for an attacker to ship inside‑wanting messages from exterior IP addresses.
An instance PowerShell command that may ship emails by way of the Direct Ship characteristic is:
Ship‑MailMessage -SmtpServer firm‑com.mail.safety.outlook.com -To joe@firm.com -From joe@firm.com -Topic "New Missed Fax‑msg" -Physique "You have got obtained a name! Click on on the hyperlink to hearken to it. Hear Now" -BodyAsHtml
This methodology works as a result of utilizing Direct Ship with the good host would not require authentication and treats the sender as inside, permitting menace actors to bypass SPF, DKIM, DMARC, and different filtering guidelines.
The e-mail campaigns impersonate voicemail or fax notifications with e-mail topics of “Caller Left VM Message.” Hooked up to the emails are PDF attachments titled ‘Fax-msg’, ‘Caller left VM Message’, ‘Play_VM-Now’, or ‘Hear’.
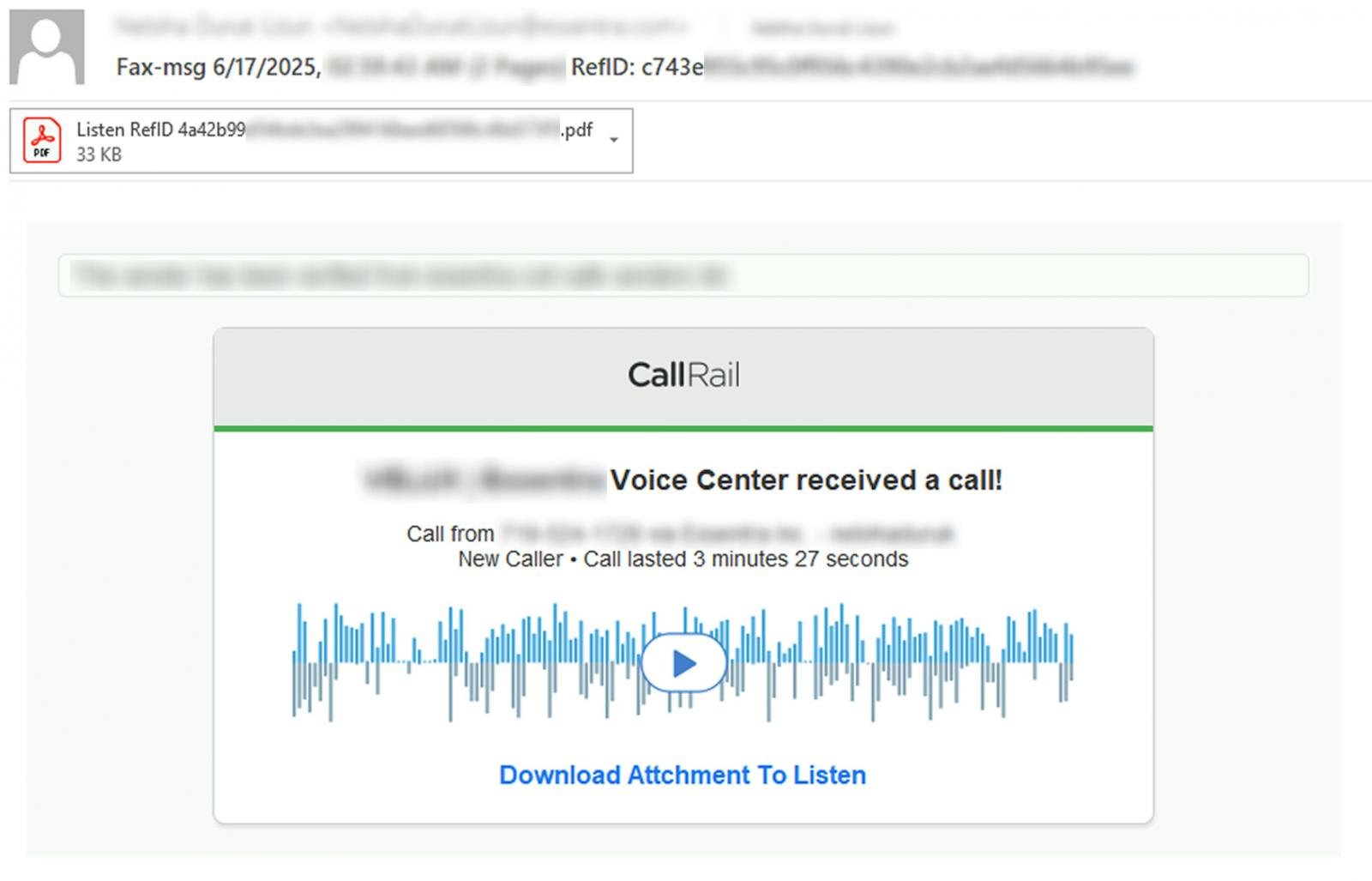
Supply: Varonis
What’s uncommon concerning the marketing campaign is that PDF attachments don’t comprise hyperlinks to the phishing pages.
As an alternative, the paperwork instruct targets to scan a QR code with their smartphone digicam to hearken to the voicemail. The PDF paperwork are additionally branded with the corporate brand to make them seem extra reputable.
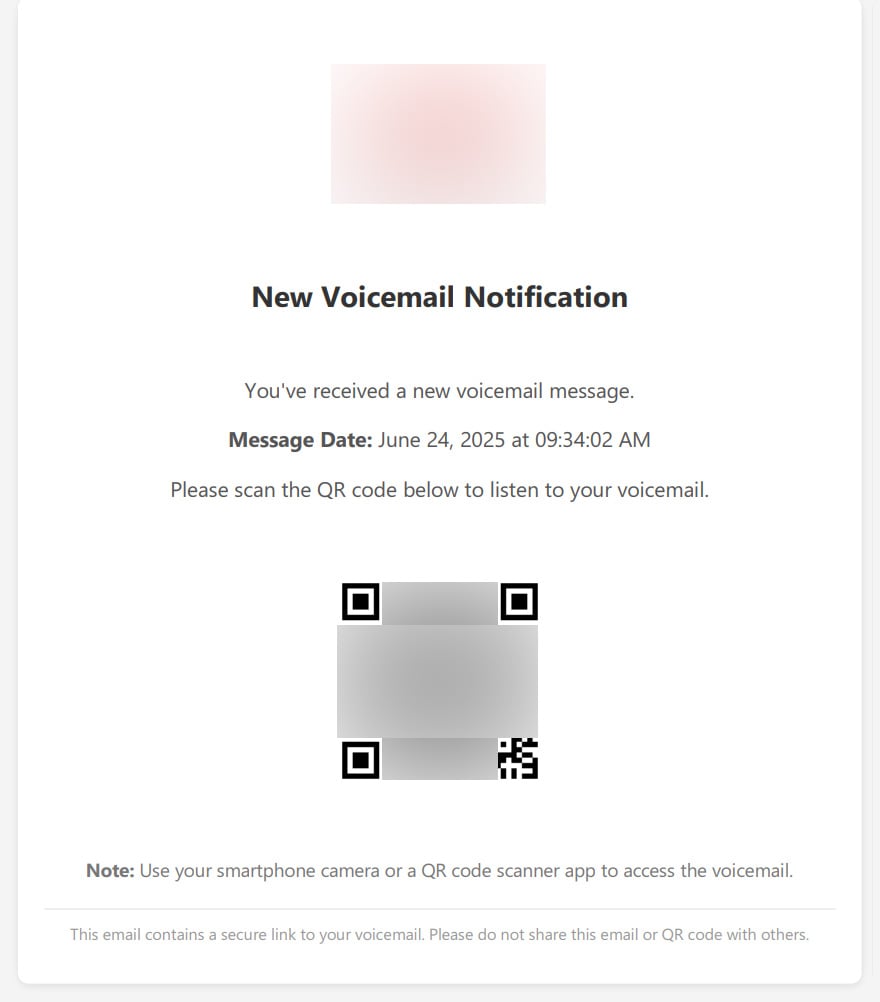
Supply: BleepingComputer
Scanning the QR code and opening the hyperlink brings you to a phishing website that shows a faux Microsoft login type, which might be used to steal the worker’s credentials.
In a single case seen by Varonis, the place an organization obtained irregular conduct alerts, the menace actors used PowerShell to ship emails via the good host from a Ukrainian IP deal with of 139.28.36[.]230 and others in the identical vary.
These messages failed SPF and DMARC checks, however they had been handled as trusted inside site visitors as a result of they got here via the inner good host.
In one other e-mail from this marketing campaign seen by BleepingComputer, the e-mail appeared to return from an inside e-mail deal with and was delivered by way of the group’s good host regardless of additionally failing SPF, DKIM, and DMARC. This e-mail originated from the IP deal with 51.89.86[.]105.
Varonis shared additional indicators of compromise (IOCs) of their report, together with domains which might be used within the marketing campaign.
Mitigating Direct Ship phishing assaults
To mitigate this menace, Varonis recommends enabling the “Reject Direct Ship” setting within the Change Admin Heart, which Microsoft launched in April 2025.
Microsoft launched this characteristic as they sometimes counsel firms allow SPF soft-fail to forestall potential routing errors. Nevertheless, this made it not possible to dam e-mail despatched by way of Direct Ship.
“Whereas SPF offers safety from spoofing of your domains, we suggest prospects use a Mushy Fail SPF configuration as a consequence of the potential of legitimate routing eventualities falling foul of SPF failures,” explains Microsoft.
“As such, no characteristic existed to dam Direct Ship site visitors for the various prospects who haven’t any want to make use of it. To this finish we now have developed the Reject Direct Ship setting for Change On-line and are saying the Public Preview for this characteristic as we speak.”
Varonis additionally recommends implementing a strict DMARC coverage (p=reject), flagging unauthenticated inside messages for overview or quarantine, imposing SPF hardfail inside Change On-line Safety, enabling Anti‑Spoofing insurance policies, and coaching staff to identify QR phishing makes an attempt.
“Direct Ship is a robust characteristic, however within the flawed palms it turns into a harmful assault vector,” concludes Varonis.
“In case you’re not actively monitoring spoofed inside emails or have not enabled these protections, now could be the time. Do not assume inside means secure.”

Patching used to imply complicated scripts, lengthy hours, and infinite fireplace drills. Not anymore.
On this new information, Tines breaks down how fashionable IT orgs are leveling up with automation. Patch sooner, cut back overhead, and concentrate on strategic work — no complicated scripts required.

